 While working on higher Impressions and views of the product page to increase the download number of my iOS app Cheat-sheets I started to deal with questions of ASO (App store optimization). App title, app description, key words are the things, that are comparably easy to set and to experiment with. But I faced a real problem with creating of good Screenshots / Images for the Cheat-sheets app.
While working on higher Impressions and views of the product page to increase the download number of my iOS app Cheat-sheets I started to deal with questions of ASO (App store optimization). App title, app description, key words are the things, that are comparably easy to set and to experiment with. But I faced a real problem with creating of good Screenshots / Images for the Cheat-sheets app.
I do realize, that App images in App store must be an eye catcher. They should attract ones attention and influence the user to push the download button. However, I’m not a designer and Photoshop is not my best friend. So I began to search for a free Screenshot generator tool. I though there might be much of them out there. But I was wrong.
First I tried Screenshot Maker at appinstitute.com. The screenshot generator has a modern intuitive interface. After uploading a screenshot it is possible to choose between particular templates, set the background color and the comment to the screenshot. Also, font and font size can be customized. Actually, it would be enough for my needs, if it worked properly. However, after exporting and downloading the generated images I was deeply disappointed. The font was set wrong and the text was on the wrong place. Beside this I noticed, that it is not possible to upload and to export images for iPad, although the option to upload iPad images is there… at least the button is displayed, which does not work. Above all is the absence of unicode support. Cheat-sheets is localized also in Russian. So, currently there is no way to make screenshots for it. Pity, very pity!
Next, I came across appscreenshot.me. It’s also a free screenshot generator. It has a pretty limited set of customization options and looks terrible 🙂 It’s not possible to design just a screenshot with a background. The uploaded image can be only embedded into iPhone frame. Screenshots for iPad cannot be designed with this generator at all. You cannot set colors as hexadecimal value, but only pick them from the color palette. For example, if you have 3 screenshots and one of them you would like update later, you’ll have to update all the 3 images, because otherwise the will look different. And at last unicode support… no unicode support, only latin letters! No commas, no spaces, no other symbols – only letters. How poor…
Unfortunately, I could not find any other free tools for creating App Store images so far. I also read about Photoshop templates and tools which automatically generate screenshots form Simulator. If I ever try these options, I’ll report about may experience in the next posts. For now I decided to try to achieve my goal with appinstitute.com. At least for iPhone images and at least for English and German languages.
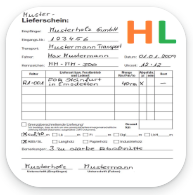

 Seit März wird die neue elektronische Lieferschein-App bei
Seit März wird die neue elektronische Lieferschein-App bei  Die Idee einer Lieferschein-App im Bereich Holzlogistik ist nicht gerade neu. Sucht man danach bei google, so wird sofort ein Dutzend Treffer angezeigt. Warum also noch eine App, wenn das Angebot ohnehin schon so groß ist? Wenn wir diese Frage nicht vom Blickwinkel des Angebots, sondern vom Blickwinkel der Anfrage betrachten, wird einiges ganz schnell klar. Die zahlreichen Unternehmen aus der Holzwirtschaft, die zu Zeiten des digitalen Wandels immer noch auf den traditionellen Lieferschein-Block und Stift setzen, haben auch recht. Das Problem ist, viele der angebotenen Apps sind entweder zu teuer, oder zu speziell, weil sie aus einer größeren Lösung “rausgerissen” sind, oder zu generell, um in der Praxis tauglich zu sein.
Die Idee einer Lieferschein-App im Bereich Holzlogistik ist nicht gerade neu. Sucht man danach bei google, so wird sofort ein Dutzend Treffer angezeigt. Warum also noch eine App, wenn das Angebot ohnehin schon so groß ist? Wenn wir diese Frage nicht vom Blickwinkel des Angebots, sondern vom Blickwinkel der Anfrage betrachten, wird einiges ganz schnell klar. Die zahlreichen Unternehmen aus der Holzwirtschaft, die zu Zeiten des digitalen Wandels immer noch auf den traditionellen Lieferschein-Block und Stift setzen, haben auch recht. Das Problem ist, viele der angebotenen Apps sind entweder zu teuer, oder zu speziell, weil sie aus einer größeren Lösung “rausgerissen” sind, oder zu generell, um in der Praxis tauglich zu sein. Was eine App ist, weiß mittlerweile jeder. Doch wie entstehen Apps? Kann wirklich jeder Apps bauen? Lasst uns einen Blick hinter die Kulisse werfen.
Was eine App ist, weiß mittlerweile jeder. Doch wie entstehen Apps? Kann wirklich jeder Apps bauen? Lasst uns einen Blick hinter die Kulisse werfen. While working on higher Impressions and views of the product page to increase the download number of my iOS app Cheat-sheets I started to deal with questions of ASO (App store optimization). App title, app description, key words are the things, that are comparably easy to set and to experiment with. But I faced a real problem with creating of good Screenshots / Images for the Cheat-sheets app.
While working on higher Impressions and views of the product page to increase the download number of my iOS app Cheat-sheets I started to deal with questions of ASO (App store optimization). App title, app description, key words are the things, that are comparably easy to set and to experiment with. But I faced a real problem with creating of good Screenshots / Images for the Cheat-sheets app. I faced the problem for the first time 2 years ago on Windows 7 computer with Internet Explorer 11. After launching skype a blanc window appeared. There were no input fields for entering user name and password. Searching for the answered in the internet revealed some interesting facts:
I faced the problem for the first time 2 years ago on Windows 7 computer with Internet Explorer 11. After launching skype a blanc window appeared. There were no input fields for entering user name and password. Searching for the answered in the internet revealed some interesting facts: Last week I had a pleasant acquaintance with Adam Giemza, head of solution architecture and security at DB Schenker AG. He asked me about Progressive web and my opinion to it. Frankly speaking, I had no opinion at all, because I’m specialized more on native apps for iOS and Android. Of course, hybrid apps, mobile first approach, responsive design are the things I heard of and had even a bit experience with them. But what are Progressive web apps? I began to read about it.
Last week I had a pleasant acquaintance with Adam Giemza, head of solution architecture and security at DB Schenker AG. He asked me about Progressive web and my opinion to it. Frankly speaking, I had no opinion at all, because I’m specialized more on native apps for iOS and Android. Of course, hybrid apps, mobile first approach, responsive design are the things I heard of and had even a bit experience with them. But what are Progressive web apps? I began to read about it. Auf Ebay Kleinanzeigen wird man fündig. Gebrauchte Lampen, Fernseher, Spielzeuge, Gartenmöbel und auch “App Programmierer”. Die letzteren werden zwar selten angeboten, dafür aber gerne gesucht.
Auf Ebay Kleinanzeigen wird man fündig. Gebrauchte Lampen, Fernseher, Spielzeuge, Gartenmöbel und auch “App Programmierer”. Die letzteren werden zwar selten angeboten, dafür aber gerne gesucht. On my MacBook Pro I have VMWare Fusion with Windows 10 installed. It worked quite well until I started getting following error message:
On my MacBook Pro I have VMWare Fusion with Windows 10 installed. It worked quite well until I started getting following error message: